Security
Cybercriminals accumulated over $2mln on crypto giveaways

In Q2 2018 Kaspersky had prevented 58K user attempts to connect to phishing websites
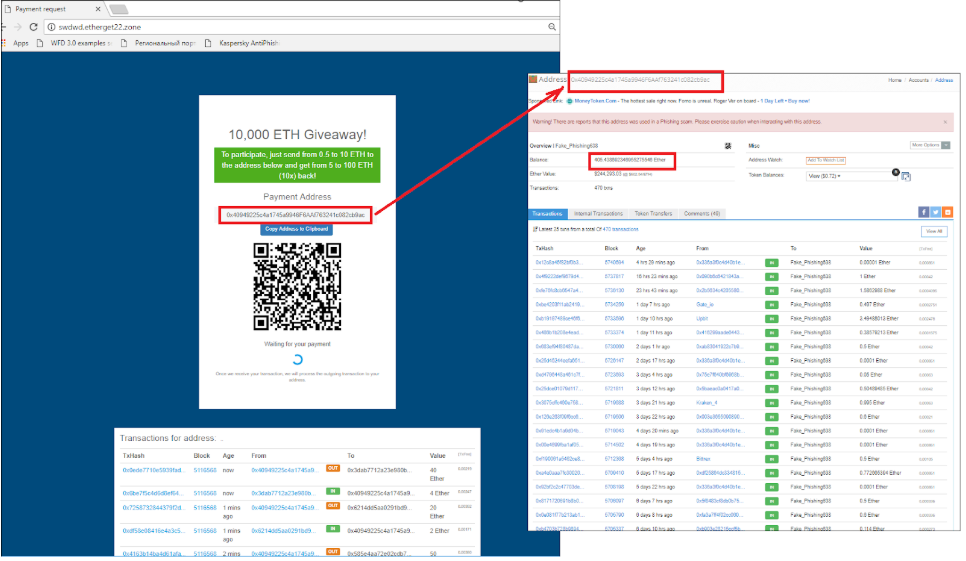
According to the report of a multinational anti-virus provider Kaspersky Lab, in Q2 2018, cybercriminals managed to make roughly $2mln on crypto-phishing activities. As the result of fake cryptocoins-giveaway events, users transferred their ETH to the specific contribution addresses and never received new tokens in return. “Please be patient,” the crooks told their victims and further to that, added that the transaction took some time to be confirmed on the blockchain.
Last week, Kaspersky Lab informed that in Q2 2018 their software had prevented 58K user attempts to connect to phishing websites. The thing is, those attempts were not only about traditional phishing that targets victims’ accounts and private key information. This time criminals pressed the crypto-button and tried to entice their victims to send them ETH voluntarily.
The crooks played the “give a bit and get a lot” string
According to the criminals’ legend, the user’s initial contribution is required for wallet verification purposes.
The story goes like this, you send your ETH to the contribution address, to verify your account. Later on, you receive more ETH in return.
To make the campaign look safe and sound, a list of ETH transactions is displayed showing how the funds of other users have already multiplied. But, in fact, it’s just a pretty picture. Never has anyone received ETH to their accounts in return.
Reportedly, the spike of fraudulent activities has to do with the nowadays context. On the verge of their popularity, ICOs on the Ethereum platform attracted phishers from different countries. Those phishers use a creative approach to make money on people’s aspiration to give a bit and get a lot.
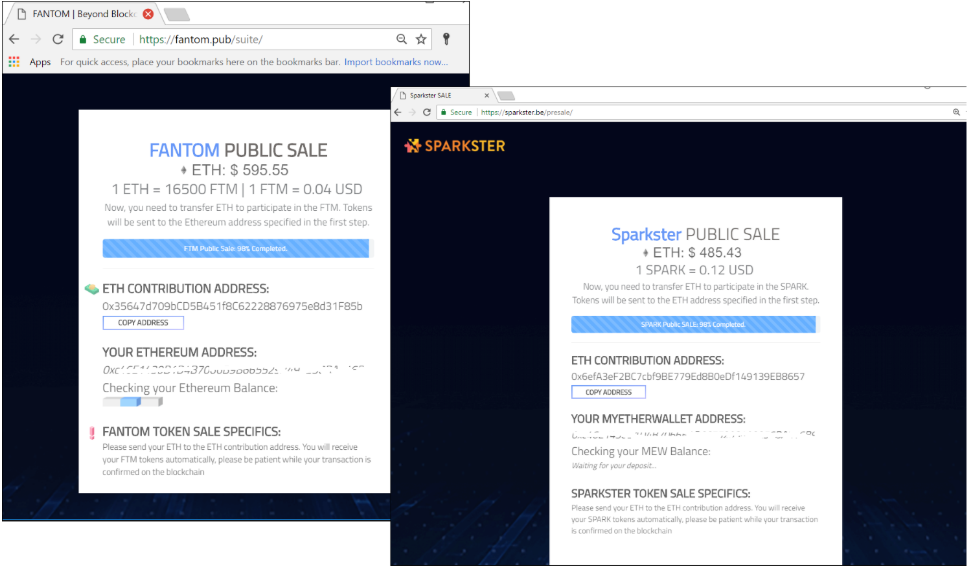
According to the report of the multinational anti-virus provider, first, criminals look for a new ICO project, then, they create a fake web environment that sounds very much familiar to that project and, right after, collect money from investors who are trying to gain early access to new tokens.
Vitalik Buterin changed his name for “Vitalik Non-giver of Ether”
The distribution channels these days also vary for phishers. Via WhatsApp unsuspecting victims voluntarily share malware links with their friends, on Google Search criminals place ads people click on. And last, but not least, crypto enthusiasts follow fake celebrities’ accounts on Twitter while they “give away” their crypto funds.
Vitalik Buterin, at some point, has even changed his name for “Vitalik Non-giver of Ether” because he was tired of scams made on his name.
Unfortunately, crypto-phishing slowly turns into the multinational trend. During the first half of 2018, Kaspersky Lab products blocked more than a hundred thousand triggers related to cryptocurrencies on fake exchanges and other sources.
British police have already warned the public about fraudulent investment schemes involving cryptocurrencies, the volume of which has led to 2mln pounds ($2.55mln) worth of losses this summer. Also, Australian consumers lost more than $2.1mln to cryptocurrency scams in 2017, the country’s Competition and Consumer Commission said.
Their weapon here is mimicking: how to detect a scam
Given that the whole world of ICOs is new and we are still trying to figure it out, it is not easy, sometimes, to identify scams, particularly for the untrained eye, which is often the case for newcomers.
You’re a target for crypto-crooks if you are an ICO investor. For ICO investors, cybercriminals create fake web pages of already existing official projects, collect your contact information and, then, send you a phishing e-mail with a number of an e-wallet you can transfer your funds to – “to invest to this ICO.” Criminals can also send the link to those pages via social media.
Their weapon here is mimicking. The crypto-crooks try their best to convince you that you’re dealing with the official project page.
Kaspersky Lab stated, the results of their research “show that cyber-criminals are adept at keeping up to date and developing their resources to achieve the best possible results in cryptocurrency phishing. These new fraud schemes are based on simple social engineering methods, but stand out from common phishing attacks because they help criminals make millions of dollars.”
According to Kaspersky Lab’s somewhat rough estimates, criminals, over the past year, managed to earn more than $10mln at the current exchange rate using the “give-away” and “fake ICO” schemes.
Here is a couple of steps, Kaspersky lab suggests, for you not to fall prey to the criminals.
- Beware of the words “free launch,” “give-away coins,” and “wallet verification.”
- If you see information about the distribution of coins on behalf of the recently hacked blockchain ecosystem, go to the official source and clarify this information
- Check if any third-parties are linked to the wallet transaction
- The addresses should be “blockchain.info,” for example, not “blackchaen.info.”
- To avoid making a mistake in the address bar and accidentally going to the phishing site instead, save the address of your e-wallet in a tab and access it from there.
Related post:
Role of Cryptocurrencies in Crime Drops by 80%
Did you find this article helpful? Don’t hesitate to share on Facebook and LinkedIn to let your network know!



F*ckin’ tremendous things here. I am very happy to see your article. Thanks a lot and i’m having a look forward to touch you. Will you kindly drop me a e-mail?
Very well written article. It will be beneficial to anyone who employess it, including me. Keep up the good work – for sure i will check out more posts.
I have been exploring for a little bit for any high quality articles or blog posts on this sort of house . Exploring in Yahoo I eventually stumbled upon this site. Studying this info So i¦m happy to express that I have an incredibly good uncanny feeling I discovered exactly what I needed. I such a lot without a doubt will make certain to do not fail to remember this site and provides it a glance on a constant basis.
I value the blog.Much thanks again. Really Great.
Can I simply say what a aid to seek out someone who truly knows what theyre speaking about on the internet. You definitely know how you can deliver a difficulty to light and make it important. Extra people need to learn this and perceive this facet of the story. I cant believe youre no more widespread because you undoubtedly have the gift.